Join our daily and weekly newsletters for the latest updates and exclusive content on industry-leading AI coverage. Learn More
National Oilwell Varco (NOV) is undergoing a sweeping cybersecurity transformation under CIO Alex Philips, embracing a Zero Trust architecture, strengthening identity defenses and infusing AI into security operations. While the journey is not complete, the results, by all accounts, are dramatic – a 35-fold drop in security events, the elimination of malware-related PC reimaging and millions saved by scrapping legacy “appliance hell” hardware.
VentureBeat recently sat down (virtually) for this in-depth interview where Philips details how NOV achieved these outcomes with Zscaler’s Zero Trust platform, aggressive identity protections and a generative AI “co-worker” for its security team.
He also shares how he keeps NOV’s board engaged on cyber risk amid a global threat landscape where 79% of attacks to gain initial access are malware-free, and adversaries can move from breach to break out in as little as 51 seconds.
Below are excerpts of Philips’ recent interview with VentureBeat:
VentureBeat: Alex, NOV went “all in” on Zero Trust a number of years ago – what were the standout gains?
Alex Philips: When we started, we were a traditional castle-and-moat model that wasn’t keeping up. We didn’t know what Zero Trust was, we just knew that we needed identity and conditional access at the core of everything. Our journey began by adopting an identity-driven architecture on Zscaler’s Zero Trust Exchange and it changed everything. Our visibility and protection coverage dramatically increased while simultaneously experiencing a 35x reduction in the number of security incidents. Before, our team was chasing thousands of malware incidents; now, it’s a tiny fraction of that. We also went from reimaging about 100 malware-infected machines each month to virtually zero now. That’s saved a considerable amount of time and money. And since the solution is cloud-based, Appliance hell is gone, as I like to say.
The zero trust approach now gives 27,500 NOV users and third parties policy-based access to thousands of internal applications, all without exposing those apps directly to the internet.
We were then able to take an interim step and re-architect our network to take advantage of internet-based connectivity vs. legacy expensive MPLS. “On average, we increased speed by 10–20x, reduced latency to critical SaaS apps, and slashed cost by over 4x… Annualized savings [from network changes] have already achieved over $6.5M,” Philips has noted of the project.
VB: How did shifting to zero trust actually reduce the security noise by such an enormous factor?
Philips: A big reason is that our internet traffic now goes through a Security Service Edge (SSE) with full SSL inspection, sandboxing, and data loss prevention. Zscaler peers directly with Microsoft, so Office 365 traffic got faster and safer – users stopped trying to bypass controls because performance improved. After being denied SSL inspection with on-prem equipment, we finally got legal approval to decrypt SSL traffic since the cloud proxy does not give NOV access to spy on the data itself. That means malware hiding in encrypted streams started getting caught before hitting endpoints. In short, we shrunk the attack surface and let good traffic flow freely. Fewer threats in meant fewer alerts overall.
John McLeod, NOV’s CISO, concurred that the “old network perimeter model doesn’t work in a hybrid world” and that an identity-centric cloud security stack was needed. By routing all enterprise traffic through cloud security layers (and even isolating risky web sessions via tools like Zscaler’s Zero Trust Browser), NOV dramatically cut down intrusion attempts. This comprehensive inspection capability is what enabled NOV to spot and stop threats that previously slipped through, slashing incident volumes by 35x.
VB: Were there any unforeseen benefits to adopting Zero Trust you didn’t initially expect?
Alex Philips: Yes, our users actually preferred the cloud-based Zero Trust experience over legacy VPN clients, so adoption was simple and gave us unprecedented agility for mobility, acquisitions, and even what we like to call “Black Swan Events”. For example, when COVID-19 hit, NOV was already prepared! I told my leadership team if all 27,500 of our users needed to work remotely, our IT systems could handle it. My leadership was stunned and our company kept moving forward without missing a beat.
VB: Identity-based attacks are on the rise – you’ve mentioned staggering stats about credential theft. How is NOV fortifying identity and access management?
Philips: Attackers know it’s often easier to log in with stolen credentials than to drop malware. In fact, 79% of attacks to gain initial access in 2024 were malware-free, relying on stolen credentials, AI-driven phishing, and deepfake scams, according to recent threat reports. One in three cloud intrusions last year involved valid credentials. We’ve tightened identity policies to make those tactics harder.
For example, we integrated our Zscaler platform with Okta for identity and conditional access checks. Our conditional access policies verify devices have our SentinelOne antivirus agent running before granting access, adding an extra posture check. We’ve also drastically limited who can perform password or MFA resets. No single admin should be able to bypass authentication controls alone. This separation of duties prevents an insider or compromised account from simply turning off our protections.
VB: You mentioned finding a gap even after disabling a user’s account. Can you explain?
Philips: We discovered that if you detect and disable a compromised user’s account, the attacker’s session tokens might still be active. It isn’t enough to reset passwords; you have to revoke session tokens to truly kick out an intruder. We’re partnering with a startup to create near real-time token invalidation solutions for our most commonly used resources. Essentially, we want to make a stolen token useless within seconds. A Zero Trust architecture helps because everything is re-authenticated through a proxy or identity provider, giving us a single choke point to cancel tokens globally. That way, even if an attacker grabs a VPN cookie or cloud session, they can’t move laterally because we’ll kill that token fast.
VB: How else are you securing identities at NOV?
Philips: We enforce multi-factor authentication (MFA) almost everywhere and monitor for abnormal access patterns. Okta, Zscaler, and SentinelOne together form an identity-driven security perimeter where each login and device posture is continuously verified. Even if someone steals a user password, they still face device checks, MFA challenges, conditional access rules, and the risk of instant session revocation if anything seems off. Resetting a password isn’t enough anymore — we must revoke session tokens instantly to stop lateral movement. That philosophy underpins NOV’s identity threat defense strategy.
VB: You’ve also been an early adopter of AI in cybersecurity. How is NOV leveraging AI and generative models in the SOC?
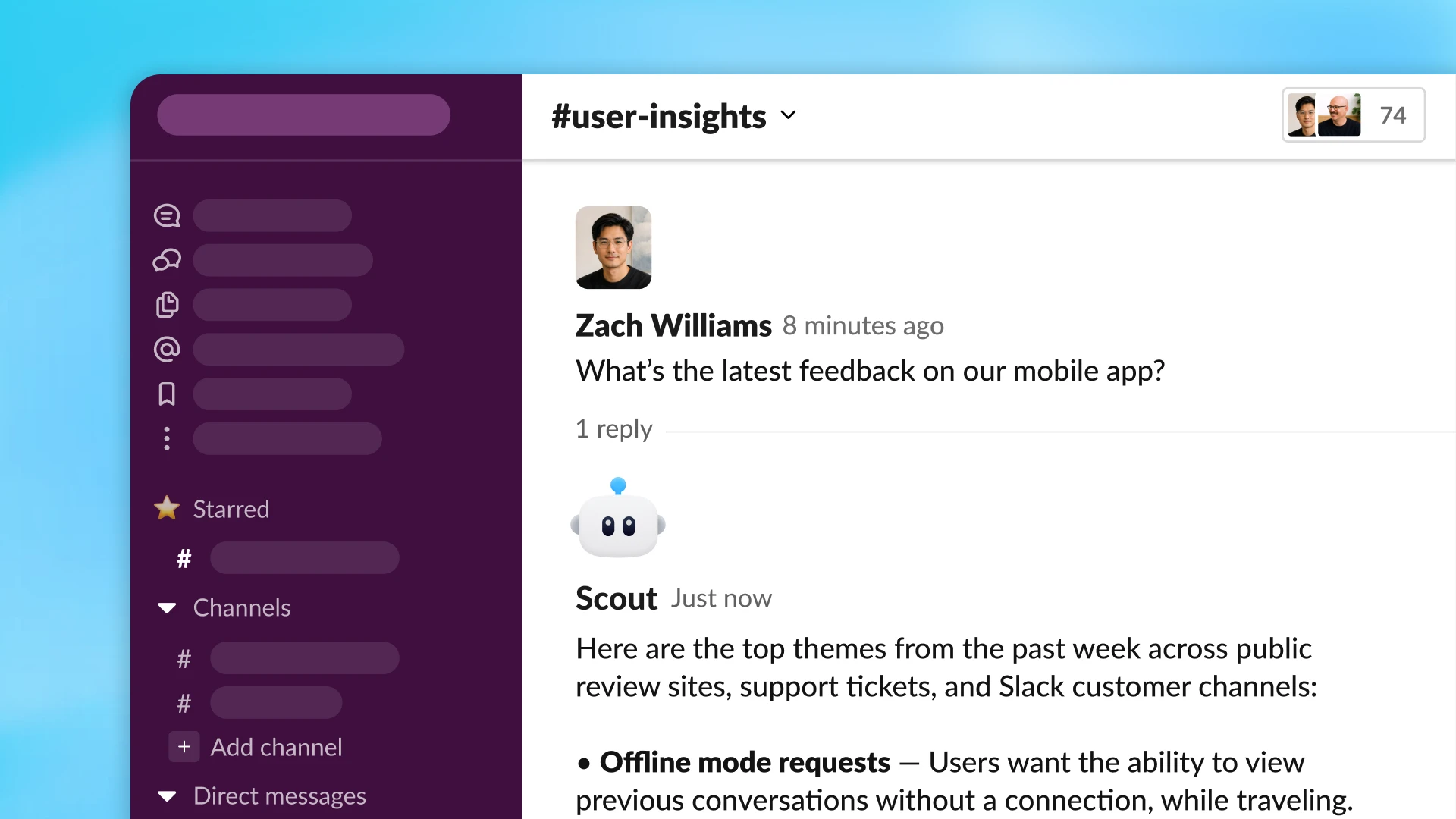
Philips: We have a relatively small security team for our global footprint, so we must work smarter. One approach is bringing AI “co-workers” into our security operations center (SOC). We partnered with SentinelOne and started using their AI security analyst tool—an AI that can write and run queries across our logs at machine speed. It’s been a game changer, allowing analysts to ask questions in plain English and get answers in seconds. Instead of manually crafting SQL queries, the AI suggests the next query or even auto-generates a report, which has dropped our mean time to respond.
We’ve seen success stories where threat hunts are performed up to 80% faster using AI assistants. Microsoft’s own data shows that adding generative AI can reduce incident mean time to resolution by 30%. Beyond vendor tools, we’re also experimenting with internal AI bots for operational analytics, using OpenAI foundational AI models to help non-technical staff quickly query data. Of course, we have data protection guardrails in place so these AI solutions don’t leak sensitive information.
VB: Cybersecurity is no longer just an IT issue. How do you engage NOV’s board and executives on cyber risk?
Philips: I made it a priority to bring our board of directors along on our cyber journey. They don’t need the deep technical minutiae, but they do need to understand our risk posture. With generative AI exploding, for example, I briefed them on both the advantages and risks early on. That education helps when I propose controls to prevent data leaks—there’s already alignment on why it’s necessary.
The board views cybersecurity as a core business risk now. They’re briefed on it at every meeting, not just once a year. We’ve even run tabletop exercises with them to show how an attack would play out, turning abstract threats into tangible decision points. That leads to stronger top-down support.
I make it a point to constantly reinforce the reality of cyber risk. Even with millions invested in our cybersecurity program, the risk is never fully eliminated. It is not if we will have an incident, but when.
VB: Any final advice, based on NOV’s journey, for other CIOs and CISOs out there?
Philips: First, recognize that security transformation and digital transformation go hand in hand. We couldn’t have moved to the cloud or enabled remote work so effectively without Zero Trust, and the business cost savings helped fund security improvements. It truly was a “win, win, win.”
Second, focus on the separation of duties in identity and access. No one person should be able to undermine your security controls—myself included. Small process changes like requiring two people to change MFA for an exec or highly privileged IT staff, can thwart malicious insiders, mistakes, and attackers.
Lastly, embrace AI carefully but proactively. AI is already a reality on the attacker side. A well-implemented AI assistant can multiply your team’s defense, but you must manage the risks of data leakage or inaccurate models. Make sure to merge AI output with your team’s skill to create an AI-infused “brAIn”.
We know the threats keep evolving, but with zero trust, strong identity security and now AI on our side, it helps give us a fighting chance.
Daily insights on business use cases with VB Daily
If you want to impress your boss, VB Daily has you covered. We give you the inside scoop on what companies are doing with generative AI, from regulatory shifts to practical deployments, so you can share insights for maximum ROI.
Read our Privacy Policy
Thanks for subscribing. Check out more VB newsletters here.
An error occured.