“Threat actors can, for pennies, cycle through IP addresses to get fresh positive-reputation IP addresses minute to minute and use them for their wares at various parts of the attack lifecycle, whether it’s brute forcing, whether it’s leveraging known positive credentials, or whether it’s exfiltrating information at the end of the attack chain,” she said.
Kimwolf: How a botnet scaled to 30 Tbps
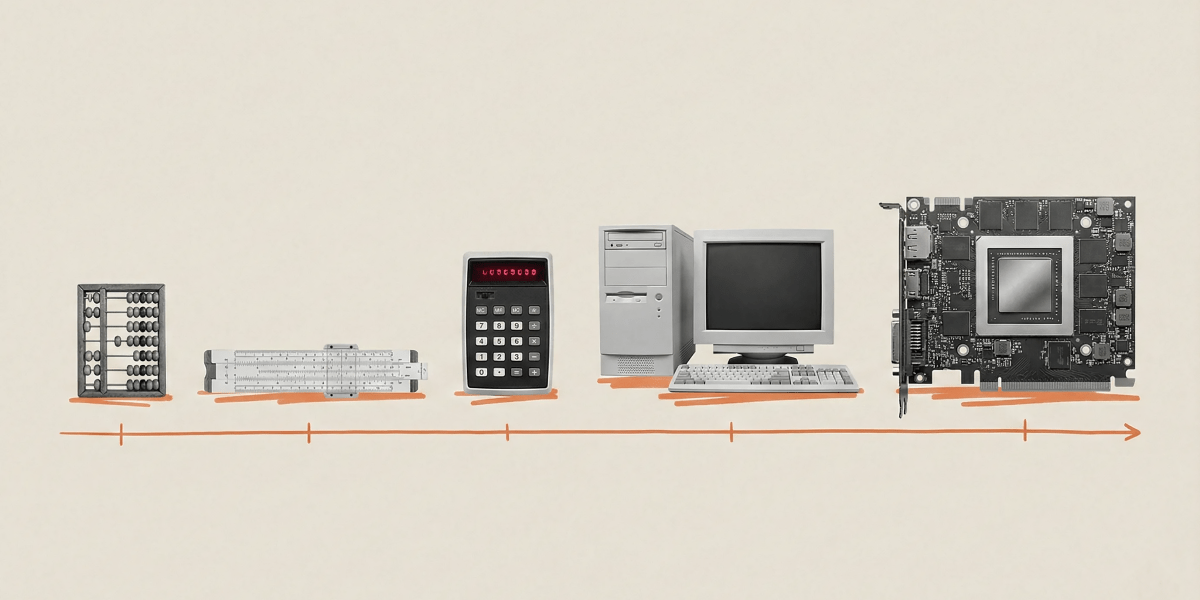
The Kimwolf botnet is the clearest illustration of what residential proxy exploitation looks like at operational scale. Kimwolf emerged in late 2025 as a breakaway from Aisuru, at the time the most powerful DDoS botnet on the internet, and ultimately launched attacks reaching 30 Tbps, roughly 30 times the largest DDoS attack observed one year earlier.
Using the network layer was critical to understanding how Kimwolf was constructed.
“We were able to identify a net new network stemming out of IPRoyal and other residential proxy networks,” Lee explained. “The Kimwolf operators were exploiting a vulnerability in IPRoyal which allowed for LAN pivoting, so a threat actor could essentially buy residential proxy access, jailbreak it, pivot out into the LAN, and recruit other devices in the LAN into their botnet.”
The architecture reflects a logistics-first approach to botnet management. C2 nodes are designed to burn quickly. When null-routing disrupts a node, operators react within hours, sometimes minutes, standing up replacements and triggering mass malware re-downloads across the botnet. Through coordinated null-routing, more than 550 Aisuru and Kimwolf C2 nodes were disrupted in four months. The speed and scale of Kimwolf’s recovery cycles show how future large-scale botnets will evolve under pressure, rebuilding faster than defenders can respond.
What defenders should do differently
The threat data tells a consistent story. Attackers are operating in spaces defenders are not watching. Edge devices go unmonitored, residential IP space is trusted by default, and indicator of compromise (IOC) lists lag weeks behind infrastructure that rotates in minutes. Closing those gaps does not require replacing existing security investments. It requires extending visibility into the parts of the network where attacks are actually staged.