And, of course, AI is now being used to speed up attacks.
Researchers at cybersecurity firm CodeWall used AI to hack into Boston Consulting Group’s data warehouse, which had no authentication on an API endpoint, allowing access to a 3-trillion-row data warehouse with individual-level employment data on hundreds of millions of people, at millions of companies. Worse yet, the service account behind that unprotected API had full write privileges, meaning that attackers would be able to change data.
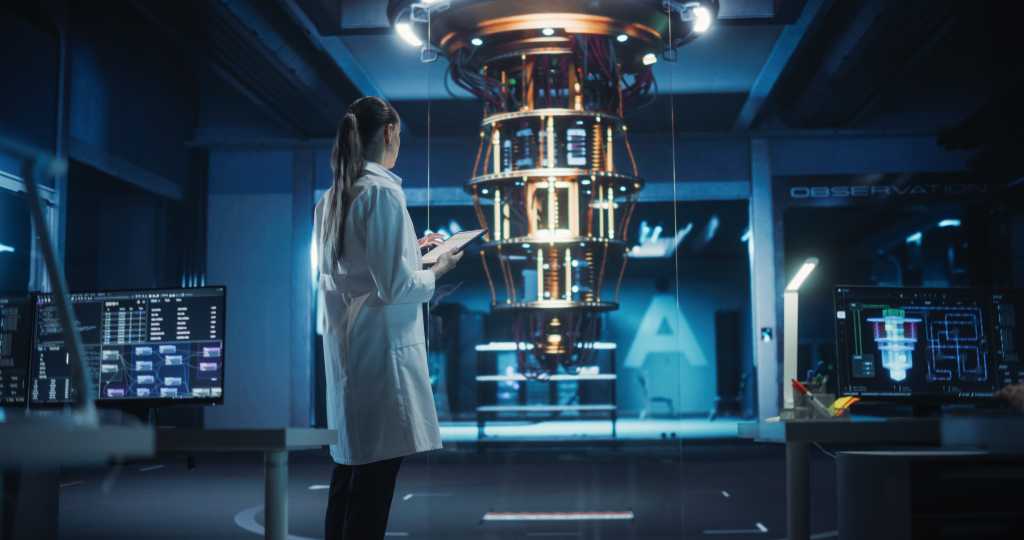
So, security managers have to figure out if they have time to deal with the quantum threat on top of everything else.
Sutor suggests that companies could take quantum preparations out of their normal cybersecurity operations. “They have to have a dedicated task force that’s maybe extra to their original budget to get post-quantum cryptography systematically deployed internally,” he says.
The latest news should be a wake-up call for companies, he adds. “Quantum is not going to steal your credit card on the web next Monday,” he says. “But now you have to say, ‘Well, maybe not Monday, but maybe three or four years from now.’”
“What I’m seeing with clients is a growing sense of urgency but not panic,” says Scott Likens, emerging technology leader at PwC. “These breakthroughs in error correction don’t mean encryption is about to be broken tomorrow, but they do reinforce that the timeline is no longer abstract.”